Wednesday 19 October 2016
Tuesday 18 October 2016
Q:How to write a resume with no job experience?
QUICK ANSWER:
To write a resume with no job experience, make an informative list, review sample resumes, and utilize available templates. Take steps to ensure your resume is formatted properly, and review all the information for accuracy. Do not include references on your resume. Make a separate reference page.
keep learning
Full Answer:
Compile a List
Compile a list of information to use for your resume. This list should include the basics, such as your name and address. It should also include your skills, related coursework and any volunteer work or awards.Review sample resumes
Review sample resumes with no work experience to help you get an idea of how yours should look.
Utilize resume templates
Using one of the resume templates available with Microsoft Word, enter the information from your list.
Ensure proper formation
Once you have added all of your information into the template, ensure proper formation. Keep the wording simple and easy to understand, and use a plain font to ensure your resume is easy to read.
Review your resume
Review your finished resume for accuracy, and have a friend or family member proofread it for accuracy.
Make a reference page
Create a separate reference page. Since you do not have professional work references, list teachers, coaches, neighbors, or family friends who can vouch for your character and ethics.
Thursday 13 October 2016
Thursday 6 October 2016
HOW TO GET A JOB (VERY EASY STEP).
Students: Applying to Google
- An updated resume
- A transcript from your university (unofficial is fine)
- In some cases, a cover letter, short essay, or additional information listed in the job description
Focus on your resume
Your resume is the first piece of information we’ll see about you. Here’s how to highlight your achievements:
- Align your skills and experience with the internship or job description
- Be specific about projects you’ve worked on or managed. What was the outcome? How did you measure success?
- If you've had a leadership role in a volunteer organization or at a part-time job, tell us about it. How big was the team? What was the scope of your work?
- Include your GPA, as well as school-related projects or coursework that demonstrate relevant skills and knowledge
- Keep it short: Aim for one page. If there’s additional information we need during the hiring process, (like a portfolio), your recruiter will work with you to collect it
Prepare for the interview process
- Once you’ve submitted your application online, our staffing team will review your resume, transcript, and any supplementary materials
- The next step in the process is a series of interviews—which may be on the phone, via video conference, or in person—to assess your skills
- For technical interviews, practice coding on a whiteboard, in Google Docs, or over the phone. You can find sample coding questions on sites like LeetCode, CodeLab, Quora, and Stack Overflow. The book “Cracking the Coding Interview” is also a good resource
- Structure your interview answers: It’s important to show how you arrive at a solution, so think out loud
Helpful questions to think about as you prepare:
- How do you work best, both as an individual and as part of a team?
- What challenges have you faced at school or at work and how did you overcome them?
- Which of your skills or experiences would be assets in the role and why?
If you don’t understand a question, ask your interviewers for clarification and take the time you need with responses.
Watch :Technical Interview Tips Click here
Wednesday 5 October 2016
Define the Turing test and its significance.
A Turing test is a test performed to determine a machine’s ability to exhibit intelligent behavior. The basic concept behind the test is that if a human judge is engaged in a natural language conversation with a computer where he cannot reliably distinguish machine from human, the machine passes the test. Responses from both participants in the conversation are received in the form of a text-only channel. This test was introduced by Alan Turing in 1950.
The Turing test is used to measure a machine's ability to think and is an important concept in the philosophy of artificial intelligence. A machine’s success at thinking can be quantified by the likelihood that a human will misidentify it as a human subject.
A computer's ability to think is determined through an imitation game. In this game, there are three players A, B and C. Player A is a man, B a woman and C is of either sex. C cannot see A and B, and communicates with the others through written notes. Player C determines which of the others is a man and which is a woman by asking a series of questions. Player A tricks the interrogator into making the wrong decision, while B attempts to guide C toward the right path.
In the original imitation game test, Turing proposes A to be a computer. The computer pretends to be a woman and tricks the interrogator into making an incorrect evaluation. The machine's success is determined by comparing the outcome of the game when A is a computer against when A is a man. If the interrogator goes wrong when playing the game between man and woman, the computer is assessed to be intelligent.
There are some variations on the interpretation of how a Turing test should be performed but the basic premise is whether a human judge can determine whether he is talking to a machine or another human.
if you wan a watch the vedio of Turing Test Then Please Click here
The Turing test is used to measure a machine's ability to think and is an important concept in the philosophy of artificial intelligence. A machine’s success at thinking can be quantified by the likelihood that a human will misidentify it as a human subject.
A computer's ability to think is determined through an imitation game. In this game, there are three players A, B and C. Player A is a man, B a woman and C is of either sex. C cannot see A and B, and communicates with the others through written notes. Player C determines which of the others is a man and which is a woman by asking a series of questions. Player A tricks the interrogator into making the wrong decision, while B attempts to guide C toward the right path.
In the original imitation game test, Turing proposes A to be a computer. The computer pretends to be a woman and tricks the interrogator into making an incorrect evaluation. The machine's success is determined by comparing the outcome of the game when A is a computer against when A is a man. If the interrogator goes wrong when playing the game between man and woman, the computer is assessed to be intelligent.
There are some variations on the interpretation of how a Turing test should be performed but the basic premise is whether a human judge can determine whether he is talking to a machine or another human.
if you wan a watch the vedio of Turing Test Then Please Click here
Define Artificial Intelligence in detail with the application areas.
Artificial intelligence (AI) is an area of computer science that emphasizes the creation of intelligent machines that work and react like humans.
Some of the activities computers with artificial intelligence are designed for include:
Some of the activities computers with artificial intelligence are designed for include:
- Speech recognition
- Learning
- Planning
- Problem solving
Research associated with artificial intelligence is highly technical and specialized. The core problems of artificial intelligence include programming computers for certain traits such as: Knowledge
aspects of the world, while computer vision is the power to analyze visual inputs with few sub-problems such as facial, object and speech recognition. Robotics is also a major field related to AI. Robots require intelligence to handle tasks such as object manipulation and navigation, along with sub-problems of localization, motion planning and mapping.
Applications of Artificial Intelligence:-
- Reasoning
- Problem solving
- Perception
- Learning
- Planning
- Ability to manipulate and move objects
Knowledge engineering is a core part of AI research. Machines can often act and react like humans only if they have abundant information relating to the world. Artificial intelligence must have access to objects, categories, properties and relations between all of them to implement knowledge engineering. Initiating common sense, reasoning and problem-solving power in machines is a difficult and tedious approach.
Machine learning is another core part of AI. Learning without any kind of supervision requires an ability to identify patterns in streams of inputs, whereas learning with adequate supervision involves classification and numerical regressions. Classification determines the category an object belongs to and regression deals with obtaining a set of numerical input or output examples, thereby discovering functions enabling the generation of suitable outputs from respective inputs. Mathematical analysis of machine learning algorithms and their performance is a well-defined branch of theoretical computer science often referred to as computational learning theory.
Machine perception deals with the capability to use sensory inputs to deduce the different
aspects of the world, while computer vision is the power to analyze visual inputs with few sub-problems such as facial, object and speech recognition. Robotics is also a major field related to AI. Robots require intelligence to handle tasks such as object manipulation and navigation, along with sub-problems of localization, motion planning and mapping.
Applications of Artificial Intelligence:-
- Problem Solving
- Game Playing
- Theorem Proving
- Natural Language Processing & Understanding
- Perception General(Speech Reorganization · Pattern Reorganization)
- Image Processing
- Expert System
- Computer Vision
- Robotics
- Intelligent Computer Assisted Instruction
- Automatic programming
- Planning & Decision Support systems
- Engineering Design & Comical Analysis
- Neural Architecture.
- Heuristic Classification.
Monday 3 October 2016
Q. Explain the concept of Class and objects. How can constructors be used in JAVA explain with a program?
Answer(its Vedio Lecture in your language)
class classname
{
Field declarations;
Methods declarations:
}
A class can contain any of the following variable types.
1.Local variables: Variables defined inside methods, constructors or blocks are called local variables. The variable will be declared and initialized within the method and the variable will be destroyed when the method has completed.
2.Instance variables: Instance variables are variables within a class but outside any method. These variables are instantiated when the class is loaded. Instance variables can be accessed from inside any method, constructor or blocks of that particular class.
3.Class variables: Class variables are variables declared with in a class, outside any method, with the static keyword. It can be tedious to initialize all of the variables in a class each time an instance is created. Because the requirement for initialization is so common, Java allows objects to initialize themselves when they are created. This automatic initialization is performed through the use of a constructor.
Creating and declaring objects;
Obtaining objects of a class in two steps
• Declare a variable of class type, it does not define an object, instead it is simply a variable that
can refer to an object. Rectangle rect1; // declare
• Declaration creates a physical copy of that object and assign it to that variable and returns
reference to it. rect1=new Rectangle(); // instantiation
Accessing class members
We can access the instance variables and the methods with the use of concerned objects and dot operator.
Obj.varaiable=value;
Obj.method(parameter list);
Constructors look a little strange because they have no return type, not even void. This is because the implicit return type of a class' constructor is the class type itself. It is the constructor's job to initialize the internal state of an object so that the code creating an instance will have a fully initialized, usable object immediately.
Example
class Box {
double width;
double height;
double depth;
// This is the constructor for Box.
Box() {
System.out.println("Constructing Box");
width = 10;
height = 10;
depth = 10;
}
// compute and return volume
double volume() {
return width * height * depth;
}
}
class BoxDemo
{
public static void main(String args[])
{
// declare, allocate, and initialize Box objects
Box mybox1 = new Box();
Box mybox2= new Box();
double vol; // get volume of first box
vol = mybox1.volume();
System.out.println("Volume is " + vol);
// get volume of second box
vol = mybox2.volume();
System.out.println("Volume is " + vol);
}
}
Class
Class is a collection of objects of same type. It provides a convenient way for packing together a group of related data items and functions. A class is declared by using a keyword class.class classname
{
Field declarations;
Methods declarations:
}
A class can contain any of the following variable types.
1.Local variables: Variables defined inside methods, constructors or blocks are called local variables. The variable will be declared and initialized within the method and the variable will be destroyed when the method has completed.
2.Instance variables: Instance variables are variables within a class but outside any method. These variables are instantiated when the class is loaded. Instance variables can be accessed from inside any method, constructor or blocks of that particular class.
3.Class variables: Class variables are variables declared with in a class, outside any method, with the static keyword. It can be tedious to initialize all of the variables in a class each time an instance is created. Because the requirement for initialization is so common, Java allows objects to initialize themselves when they are created. This automatic initialization is performed through the use of a constructor.
Creating and declaring objects;
Obtaining objects of a class in two steps
• Declare a variable of class type, it does not define an object, instead it is simply a variable that
can refer to an object. Rectangle rect1; // declare
• Declaration creates a physical copy of that object and assign it to that variable and returns
reference to it. rect1=new Rectangle(); // instantiation
Accessing class members
We can access the instance variables and the methods with the use of concerned objects and dot operator.
Obj.varaiable=value;
Obj.method(parameter list);
Constructors
A constructor initializes an object immediately upon creation. It has the same name as the class in which it resides and is syntactically similar to a method. Once defined, the constructor is automatically called immediately after the object is created, before the new operator completes.Constructors look a little strange because they have no return type, not even void. This is because the implicit return type of a class' constructor is the class type itself. It is the constructor's job to initialize the internal state of an object so that the code creating an instance will have a fully initialized, usable object immediately.
Example
class Box {
double width;
double height;
double depth;
// This is the constructor for Box.
Box() {
System.out.println("Constructing Box");
width = 10;
height = 10;
depth = 10;
}
// compute and return volume
double volume() {
return width * height * depth;
}
}
class BoxDemo
{
public static void main(String args[])
{
// declare, allocate, and initialize Box objects
Box mybox1 = new Box();
Box mybox2= new Box();
double vol; // get volume of first box
vol = mybox1.volume();
System.out.println("Volume is " + vol);
// get volume of second box
vol = mybox2.volume();
System.out.println("Volume is " + vol);
}
}
Q. Explain different types of Selection Control statements in JAVA with syntax. Write a program in JAVA to find the greatest number among three given numbers. Your program should take input from the user.
Answer
Control Statements
The statements inside your source files are generally executed from top to bottom, in the order that they appear Control flow statements, however, break up the flow of execution by employing decision making, looping, and branching, enabling your program to conditionally execute particular blocks of code. ava contains the following types of control statements:
1- Selection Statements
2- Repetition Statements
3- Branching Statements
Selection statements
If Statement:
This is a control statement to execute a single statement or a block of code, when the given condition is true and if it is false then it skips if block and rest code of program is executed .
Syntax:
if(conditional_expression){
<statements>;
...;
...;
}
If-else Statement:
The "if-else" statement is an extension of if statement that provides another option when 'if' statement
evaluates to "false" i.e. else block is executed if "if" statement is false.
Syntax: if(conditional_expression){
<statements>;
...;
...; }
else{ <statements>;
....;
....;
}
Switch Statement:
This is an easier implementation to the if-else statements. The keyword "switch" is followed by an expression
that should evaluates to byte, short, char or int primitive data types ,only. In a switch block there can be one
or more labeled cases. The expression that creates labels for the case must be unique. The switch expression
is matched with each case label. Only the matched case is executed ,if no case matches then the default
statement (if present) is executed.
Syntax:
switch(control_expression){ case
expression 1: <statement>; case
expression 2: <statement>;
...
... case expression n:
<statement>; default:
<statement>;
}//end switch
Write a program in JAVA to find the greatest number among three given numbers. Your program should take input from the user
Answer.
import java.io.*;
class GreatestNumber
{
public static void main(String args[]) throws java.lang.Exception
{
int n1,n2,n3;
BufferedReader buffer = new BufferedReader (new InputStreamReader(System.in));
System.out.println("Enter First number");
n1=Integer.parseInt(buffer.readLine());
System.out.println("Enter Second number");
n2=Integer.parseInt(buffer.readLine());
System.out.println("Enter Third number");
n3=Integer.parseInt(buffer.readLine());
if(n1>n2)
{
if(n1>n3)
{
System.out.println("n1 = "+n1+" is greater");
}
else
{
System.out.println("n3 = "+n3+" is greater");
}
}
else
{
if(n2>n3)
{
System.out.println("n2 = "+n2+" is greater");
}
else
{
System.out.println("n3 = "+n3+" is greater");
}
}
}
}
sos
Control Statements
The statements inside your source files are generally executed from top to bottom, in the order that they appear Control flow statements, however, break up the flow of execution by employing decision making, looping, and branching, enabling your program to conditionally execute particular blocks of code. ava contains the following types of control statements:
1- Selection Statements
2- Repetition Statements
3- Branching Statements
Selection statements
If Statement:
This is a control statement to execute a single statement or a block of code, when the given condition is true and if it is false then it skips if block and rest code of program is executed .
Syntax:
if(conditional_expression){
<statements>;
...;
...;
}
If-else Statement:
The "if-else" statement is an extension of if statement that provides another option when 'if' statement
evaluates to "false" i.e. else block is executed if "if" statement is false.
Syntax: if(conditional_expression){
<statements>;
...;
...; }
else{ <statements>;
....;
....;
}
Switch Statement:
This is an easier implementation to the if-else statements. The keyword "switch" is followed by an expression
that should evaluates to byte, short, char or int primitive data types ,only. In a switch block there can be one
or more labeled cases. The expression that creates labels for the case must be unique. The switch expression
is matched with each case label. Only the matched case is executed ,if no case matches then the default
statement (if present) is executed.
Syntax:
switch(control_expression){ case
expression 1: <statement>; case
expression 2: <statement>;
...
... case expression n:
<statement>; default:
<statement>;
}//end switch
Write a program in JAVA to find the greatest number among three given numbers. Your program should take input from the user
Answer.
import java.io.*;
class GreatestNumber
{
public static void main(String args[]) throws java.lang.Exception
{
int n1,n2,n3;
BufferedReader buffer = new BufferedReader (new InputStreamReader(System.in));
System.out.println("Enter First number");
n1=Integer.parseInt(buffer.readLine());
System.out.println("Enter Second number");
n2=Integer.parseInt(buffer.readLine());
System.out.println("Enter Third number");
n3=Integer.parseInt(buffer.readLine());
if(n1>n2)
{
if(n1>n3)
{
System.out.println("n1 = "+n1+" is greater");
}
else
{
System.out.println("n3 = "+n3+" is greater");
}
}
else
{
if(n2>n3)
{
System.out.println("n2 = "+n2+" is greater");
}
else
{
System.out.println("n3 = "+n3+" is greater");
}
}
}
}
sos
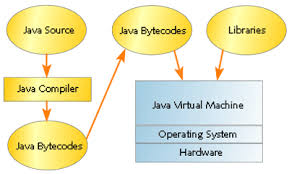
Q . Write features of JAVA programming language in details. What do you understand by bytecode? Also write working of JVM.
Answer.
Java is a general-purpose, high-level programming language. The features of Java:
• Java program is both compiled and interpreted.
• Write once, run anywhere
Java is a software-only platform running on top of other, hardware-based platforms.
• Java Virtual Machine (Java VM)
• The Java Application Programming Interface
(JAVA API)
Features of Java
(1) Simple: It fixes some clumsy features of C++. There is no use of pointers. Java has Automatic garbage
collection. It has rich pre-defined class library http://java.sun.com/j2se/1.4.2/docs/api/
(2) Object oriented: Focus on the data (objects) and methods manipulating the data. All functions are associated with objects. Almost all datatypes are objects (files, strings, etc.). it has potentially better code organization and reuse.
(3) Interpreted: Java compiler generate byte-codes, not native machine code. This compiled byte-codes are platform-independent. Java bytecodes are translated on the fly to machine readable instructions in runtime (Java Virtual Machine).
(4) Portable: Same application runs on all platforms. The sizes of the primitive data types are always the same. The libraries define portable interfaces
(5) Reliable: There is extensive compile-time and runtime error checking. No pointers but real arrays. Memory corruptions or unauthorized memory accesses are impossible. Automatic garbage collection tracks objects usage over time.
(6) Secure: Its usage in networked environments requires more security. Memory allocation model is a major defense. Here access restrictions are forced (private, public).
(7) Multi-threaded: Multiple concurrent threads of executions can run simultaneously. It utilizes a
sophisticated set of synchronization primitives (based on monitors and condition variables paradigm) to achieve this
(8) Dynamic: Java is designed to adapt to evolving environment. Libraries can freely add new methods and instance variables without any effect on their clients. Interfaces promote flexibility and reusability in code by specifying a set of methods an object can perform, but leaves open how these methods should be implemented. It can check the class type in runtime.
ByteCode
Java compilation produces “bytecode” which is an Intermediate code readable by the VM and transferable across the Internet as applets. VM interprets BC into instructions. ByteCode produced on any platform may be executed on any other platform which supports a VM.
JVM
Acts as an interpreter for the bytecode, which takes the bytecodes as input and executes as if it was a physical process executing machine code. JVM is a component of the Java system that interprets and executes the instructions in our class files. Each instance of the JVM has one method area, one heap, and one or more stacks - one for each thread.
• When JVM loads a class file, it puts its information in the method area
• As the program runs, all objects instantiated are stored in the heap
• The stack area is used to store activation records as a program runs
Java is a general-purpose, high-level programming language. The features of Java:
• Java program is both compiled and interpreted.
• Write once, run anywhere
Java is a software-only platform running on top of other, hardware-based platforms.
• Java Virtual Machine (Java VM)
• The Java Application Programming Interface
(JAVA API)
Features of Java
(1) Simple: It fixes some clumsy features of C++. There is no use of pointers. Java has Automatic garbage
collection. It has rich pre-defined class library http://java.sun.com/j2se/1.4.2/docs/api/
(2) Object oriented: Focus on the data (objects) and methods manipulating the data. All functions are associated with objects. Almost all datatypes are objects (files, strings, etc.). it has potentially better code organization and reuse.
(3) Interpreted: Java compiler generate byte-codes, not native machine code. This compiled byte-codes are platform-independent. Java bytecodes are translated on the fly to machine readable instructions in runtime (Java Virtual Machine).
(4) Portable: Same application runs on all platforms. The sizes of the primitive data types are always the same. The libraries define portable interfaces
(5) Reliable: There is extensive compile-time and runtime error checking. No pointers but real arrays. Memory corruptions or unauthorized memory accesses are impossible. Automatic garbage collection tracks objects usage over time.
(6) Secure: Its usage in networked environments requires more security. Memory allocation model is a major defense. Here access restrictions are forced (private, public).
(7) Multi-threaded: Multiple concurrent threads of executions can run simultaneously. It utilizes a
sophisticated set of synchronization primitives (based on monitors and condition variables paradigm) to achieve this
(8) Dynamic: Java is designed to adapt to evolving environment. Libraries can freely add new methods and instance variables without any effect on their clients. Interfaces promote flexibility and reusability in code by specifying a set of methods an object can perform, but leaves open how these methods should be implemented. It can check the class type in runtime.
ByteCode
Java compilation produces “bytecode” which is an Intermediate code readable by the VM and transferable across the Internet as applets. VM interprets BC into instructions. ByteCode produced on any platform may be executed on any other platform which supports a VM.
JVM
Acts as an interpreter for the bytecode, which takes the bytecodes as input and executes as if it was a physical process executing machine code. JVM is a component of the Java system that interprets and executes the instructions in our class files. Each instance of the JVM has one method area, one heap, and one or more stacks - one for each thread.
• When JVM loads a class file, it puts its information in the method area
• As the program runs, all objects instantiated are stored in the heap
• The stack area is used to store activation records as a program runs
Q . Draw and Explain TCP/IP protocol suite in detail.
Answer
The Internet Protocol suite like many protocol suites can be viewed as a set of layers. Each layer solves a set of problems involving the transmission of data, and provides a well-defined service to the upper layer protocols based on using services from some lower layers. Upper layers are logically closer to the user and deal with more abstract data, relying on lower layer protocols to translate data into forms that can eventually be physically transmitted. The TCP/IP model consists of four layers.
From lowest to highest, these are the Link Layer, the Internet Layer, the Transport Layer, and the Application Layer.
The main differences between the OSI architecture and that of TCP/IP relate to the layers above the transport layer (layer 4) and those at the network layer (layer 3). OSI has both, the session layer and the presentation layer, whereas TCP/IP combines both into an application layer. The requirement for a connectionless protocol also required TCP/IP to combine OSI’s physical layer and data link layer into a network level.
The subnet protocol consists of the IMP-IMP protocol which aims to provide a reliable connection between neighboured IMPs. For Ethernet based networks e.g. LANs (Local Area Network), the data link protocol LLC (Logical Link Control) is equally used in OSI and TCP/IP networks.
The OSI transport layer protocol (TP4) and the internet tranport protocol (TCP) have many similarities but also some remarkable differences. Both protocols are built to provide a reliable connection oriented end-toend transport service on top of an unreliable network service. The network service may loose packets, store them, deliver them in the wrong order or even duplicate packets. Both protocols have to be able to deal with the most severe problems e.g. a subnetwork stores valid packets and sends them at a later date. TP4 and TCP have a connect, transfer and a disconnect phase. The principles of doing this are also quite similar.
TCP/IP Protocol Suite
The Internet Protocol suite (commonly TCP/IP) is the set of communications protocols used for the Internet and other similar networks. It is named from two of the most important protocols in it: the Transmission Control Protocol (TCP) and the Internet Protocol (IP), which were the first two networking protocols defined in this standard. Today's IP networking represents a synthesis of several developments that began to evolve in the 1960s and 1970s, namely the Internet and LANs (Local Area Networks), which, together with the invention of the World Wide Web by Sir Tim Berners-Lee in 1989, have revolutionized computing.The Internet Protocol suite like many protocol suites can be viewed as a set of layers. Each layer solves a set of problems involving the transmission of data, and provides a well-defined service to the upper layer protocols based on using services from some lower layers. Upper layers are logically closer to the user and deal with more abstract data, relying on lower layer protocols to translate data into forms that can eventually be physically transmitted. The TCP/IP model consists of four layers.
From lowest to highest, these are the Link Layer, the Internet Layer, the Transport Layer, and the Application Layer.
The main differences between the OSI architecture and that of TCP/IP relate to the layers above the transport layer (layer 4) and those at the network layer (layer 3). OSI has both, the session layer and the presentation layer, whereas TCP/IP combines both into an application layer. The requirement for a connectionless protocol also required TCP/IP to combine OSI’s physical layer and data link layer into a network level.
1. Physical Layer
The physical layer may be either ethernet, SDH-DCC, or some timeslot of a PDH signal. Either OSI protocols and TCP/IP protocols build on the same physical layer standards, thus there is no difference between OSI and TCP/IP in this aspect.2. Data Link Layer
The purpose of the data link layer is to provide error free data transmission even on noisy links. This is achieved by framing of data and retransmission of every frame until it is acknowledged from the far end, using flow control mechanisms. Error detection is done by means of error detection codes. In the internet world there is no real data link layer protocol, but the subnet protocol which has quite many similarities.The subnet protocol consists of the IMP-IMP protocol which aims to provide a reliable connection between neighboured IMPs. For Ethernet based networks e.g. LANs (Local Area Network), the data link protocol LLC (Logical Link Control) is equally used in OSI and TCP/IP networks.
3. Network Layer
The network layer provides routing capabilities between source and destination system. TCP divides messages in datagrams of up to 64k length. Each datagram consists of a header and a text part. Besides some other information, the header contains the source and the destination address of the datagram. IP routes these datagrams through the network using e.g. the protocol OSPF (Open Shortest Path First) or RIP (Route Information Protocol) for path calculation purposes. The service provided by IP is not reliable. Datagrams may be received in the wrong order or they may even get lost in the network.4. Transport Layer
The transport layer provides a reliable end-to-end connection between source and destination system on top of the network layer. It builds an integral part of the whole OSI layering principle and of the internet protocol.The OSI transport layer protocol (TP4) and the internet tranport protocol (TCP) have many similarities but also some remarkable differences. Both protocols are built to provide a reliable connection oriented end-toend transport service on top of an unreliable network service. The network service may loose packets, store them, deliver them in the wrong order or even duplicate packets. Both protocols have to be able to deal with the most severe problems e.g. a subnetwork stores valid packets and sends them at a later date. TP4 and TCP have a connect, transfer and a disconnect phase. The principles of doing this are also quite similar.
Q 1. What do you understand by Internet? Explain concept of IP address in detail.
Answer.
The Internet is a worldwide system of computer networks - a network of networks in which users at any one
computer can, if they have permission, get information from any other computer (and sometimes talk directly
to users at other computers). It was conceived by the Advanced Research Projects Agency (ARPA) of the U.S.
government in 1969 and was first known as the ARPANET. The original aim was to create a network that
would allow users of a research computer at one university to be able to "talk to" research computers at other
universities. A side benefit of ARPANet's design was that, because messages could be routed or rerouted in
more than one direction, the network could continue to function even if parts of it were destroyed in the event
of a military attack or other disaster.
Today, the Internet is a public, cooperative, and self-sustaining facility accessible to hundreds of millions of
people worldwide. Physically, the Internet uses a portion of the total resources of the currently existing public
telecommunication networks. Technically, what distinguishes the Internet is its use of a set of protocols called
TCP/IP (for Transmission Control Protocol/Internet Protocol). Two recent adaptations of Internet technology,
the intranet and the extranet, also make use of the TCP/IP protocol.
Common methods of home access include dial-up, landline broadband (over coaxial cable, fiber optic or
copper wires), Wi-Fi, satellite and 3G technology cell phones.
An Internet Protocol (IP) address is a numerical identification (logical address) that is assigned to devices participating in a computer network utilizing the Internet Protocol for communication between its nodes. Although IP addresses are stored as binary numbers, they are often displayed in more human-readable notations, such as 192.168.100.1 (for IPv4), and 2001:db8:0:1234:0:567:1:1 (for IPv6). The role of the IP address has been characterized as follows: "A name indicates what we seek. An address indicates where it is. A route indicates how to get there." Originally, an IP address was defined as a 32-bit number and this system, now named Internet Protocol Version 4 (IPv4), is still in use today. However, due to the enormous growth of the Internet and the resulting depletion of the address space, a new addressing system (IPv6), using 128 bits for the address, had to be developed. IPv6 is now being deployed across the world; in many places it coexists with the old standard and is transmitted over the same hardware and network links.
The Internet Protocol also is responsible for routing data packets between networks, and IP addresses specify the locations of the source and destination nodes in the topology of the routing system. For this purpose, some of the bits in an IP address are used to designate a sub network. (In CIDR notation, the number of bits used for the subnet follows the IP address. E.g. 192.168.100.1/16) An IP address can be private, for use on a LAN, or public, for use on the Internet or other WAN.
Some of the Web browsers currently available for personal computers include Mozilla Firefox, Safari, Konqueror, Opera, Flock, Internet Explorer, Epiphany and AOL Explorer. Web browsers are the most commonly used type of HTTP user agent. Although browsers are typically used to access the World Wide Web, they can also be used to access information provided by Web servers in private networks or content in file systems.
They work with addresses in following way:
• When we give a name of webpage to open
• The web browser send it to the attached DNS server
• If its lookup table has the corresponding ip, it returns or forward it to the next DNS server
• When browser get corresponding ip for the name provided to try to download the index page or the
mentioned page
• When it gets downloaded then browser interprets the code and displays it.
Internet
The Internet is a worldwide system of computer networks - a network of networks in which users at any one
computer can, if they have permission, get information from any other computer (and sometimes talk directly
to users at other computers). It was conceived by the Advanced Research Projects Agency (ARPA) of the U.S.
government in 1969 and was first known as the ARPANET. The original aim was to create a network that
would allow users of a research computer at one university to be able to "talk to" research computers at other
universities. A side benefit of ARPANet's design was that, because messages could be routed or rerouted in
more than one direction, the network could continue to function even if parts of it were destroyed in the event
of a military attack or other disaster.
Today, the Internet is a public, cooperative, and self-sustaining facility accessible to hundreds of millions of
people worldwide. Physically, the Internet uses a portion of the total resources of the currently existing public
telecommunication networks. Technically, what distinguishes the Internet is its use of a set of protocols called
TCP/IP (for Transmission Control Protocol/Internet Protocol). Two recent adaptations of Internet technology,
the intranet and the extranet, also make use of the TCP/IP protocol.
Common methods of home access include dial-up, landline broadband (over coaxial cable, fiber optic or
copper wires), Wi-Fi, satellite and 3G technology cell phones.
IP Addresses
The Internet Protocol also is responsible for routing data packets between networks, and IP addresses specify the locations of the source and destination nodes in the topology of the routing system. For this purpose, some of the bits in an IP address are used to designate a sub network. (In CIDR notation, the number of bits used for the subnet follows the IP address. E.g. 192.168.100.1/16) An IP address can be private, for use on a LAN, or public, for use on the Internet or other WAN.
Working of web browsers with these addresses.
A web browser is a software application which enables a user to display and interact with text, images, videos, music and other information typically located on a Web page at a website on the World Wide Web or a local area network. Text and images on a Web page can contain hyperlinks to other Web pages at the same or different website. Web browsers allow a user for quick and easy access information provided on many Web pages at many websites by traversing these links.Some of the Web browsers currently available for personal computers include Mozilla Firefox, Safari, Konqueror, Opera, Flock, Internet Explorer, Epiphany and AOL Explorer. Web browsers are the most commonly used type of HTTP user agent. Although browsers are typically used to access the World Wide Web, they can also be used to access information provided by Web servers in private networks or content in file systems.
They work with addresses in following way:
• When we give a name of webpage to open
• The web browser send it to the attached DNS server
• If its lookup table has the corresponding ip, it returns or forward it to the next DNS server
• When browser get corresponding ip for the name provided to try to download the index page or the
mentioned page
• When it gets downloaded then browser interprets the code and displays it.
Subscribe to:
Posts (Atom)